The Alu Uses to Hold Data That Is Being Processed.
In such cases the timeline may be partially rendered. The PCR extension mechanism is crucial to establishing a Chain of trust in layers of software see.

Chapter 3 Using Verbs Correctly Verb Worksheets Verb Chapter
Another example of computer crime is cracking in which the cracker decodes or breaks the codes that are designed to protect data.

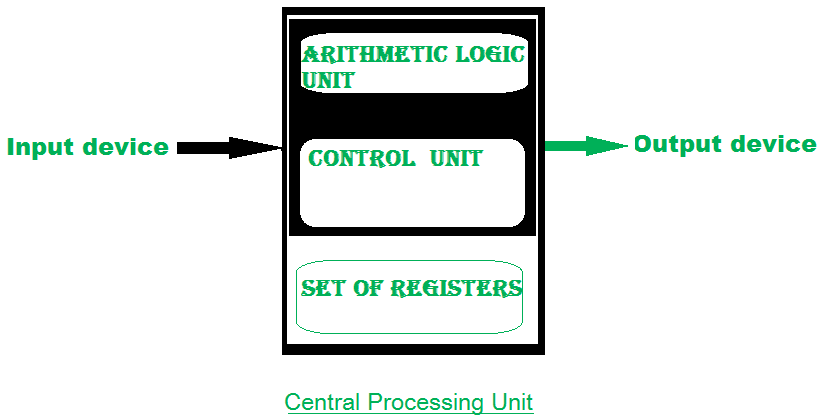
. Control facilitates orderly routing of data including IO to the ALUs external environment eg peripheral devices such as disk or keyboard. Therefore if any module being measured has been modified the resulting PCR measurement will be different and thus it is easy to detect if any code configuration data etc. The program or script which is used to break the security is known as crack.
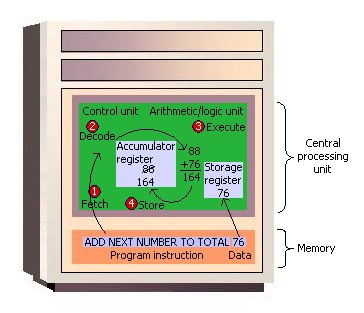
A computer program in its human-readable form is called source codeSource code needs another computer program to execute because computers can only. After being processed the information is sent to. Likewise when the time is right the control unit sends these items from memory to the arithmeticlogic unit where an arithmetic operation or logical operation is performed.
A cracker is an individual who uses a script or program to decipher codes or breakdown security systems for illegal activities. How do data and instructions get from an input device into memory. Intel TXT uses a Trusted Platform Module.
In declarative programming a computer program is a set of instructions. It is an electronic circuit that combines different arithmetic and bitwise logic operations. The integration of Internet Explorer with the dominant Windows operating system was the turning point in what came to be known as the.
There may not be room in memory to hold the processed data. What is it called. The acronym stands for Arithmetic-Logic-Unit.
At the same time a spinning circle replaces the icon of the current session tab indicating the timeline is not fully. The ALU and control unit of most of the microcomputers are combined and manufacture on a single silicon chip. That has been measured had been altered or corrupted.
The profiler loads the timeline gradually as it reads the data. The very basic functionality that each ALU has to have otherwise it wouldnt make any sense is the arithmetic addition and the logic-functions AND and NOT or OR and NOT as they are complete which means that you can derive. Basic ISA cycle where fetch gets operands from memory decode translates the operands into a format the ALU can accept and execute performs an ALU operation on the decoded operands - adapted from Maf01 212.
The control unit sends them. In imperative programming a computer program is a sequence of instructions in a programming language that a computer can execute or interpret. This is more apparent if the data file being loaded is big or the application has generated a lot of data.
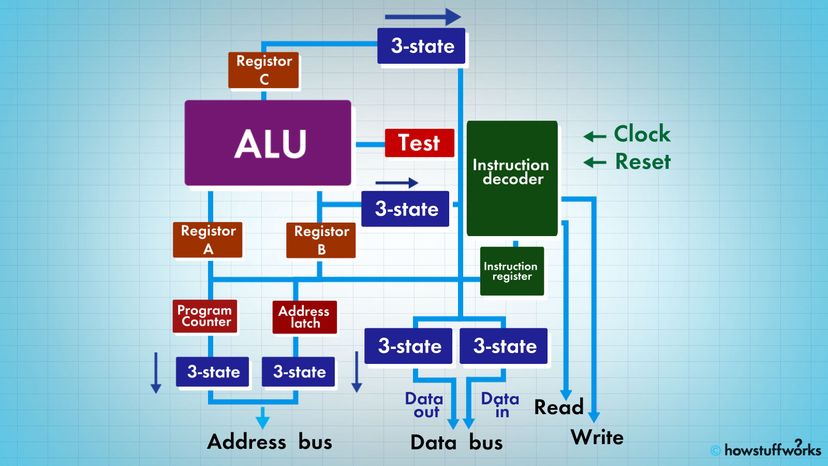
How Microprocessors Work Howstuffworks

Arithmetic Logic Unit An Overview Sciencedirect Topics
Introduction Of Alu And Data Path Geeksforgeeks

1 Page Case Study Example In 2021 Case Study Essay Writing Tips Essay Examples

Accumulator Register An Overview Sciencedirect Topics

Von Neumann Architecture The Reference Model For Computer Computer Architecture Electrical Symbols Architecture

Fire Movement Facts Stock Market Quotes Financial News Stock Market

Arithmetic Logic Unit An Overview Sciencedirect Topics

Arithmetic Logic Unit An Overview Sciencedirect Topics
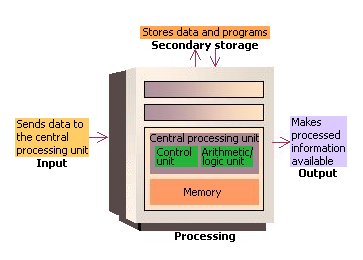
How The Computer Works The Cpu And Memory
How The Computer Works The Cpu And Memory
How The Computer Works The Cpu And Memory

Used To Start And Function The Computer The Unit Computer System System

Insplosion Janelas Janelas Lindas Portas De Entrada
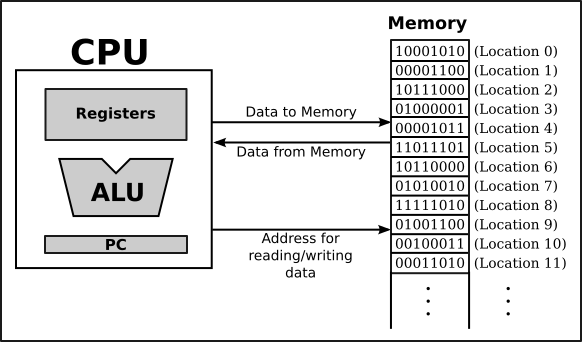
Javanotes 8 1 3 Section 1 1 The Fetch And Execute Cycle Machine Language
Organization Of Computer Systems Processor Datapath

To Work With Microprocessor 8085 First We Have To Know The Internal Architecture Of 8085 Microproces In 2021 Computer Architecture Electronic Engineering Logic Design

Comments
Post a Comment